Best Ways to Share Files in SharePoint
How to Share Files in SharePoint: Top Methods and Best Practices
SharePoint has evolved from a traditional document management system into the backbone of the modern digital workplace. Within the Microsoft 365 ecosystem, it serves as the centralized engine for content storage, collaboration, and governance. Whether an organization is small or a global enterprise, the ability to distribute information effectively while maintaining security is paramount. File sharing is not merely a feature of SharePoint; it is the core functionality that enables remote teams to collaborate in real-time, facilitates seamless communication with external partners, and ensures that institutional knowledge is accessible to those who need it.
In the current landscape of hybrid and remote work, the demand for flexible yet secure sharing has never been higher. Users expect the ability to send a document to a colleague or client with a few clicks, similar to personal cloud services, but with the added layers of corporate security and compliance. This article provides a comprehensive exploration of the various methods available for sharing files within SharePoint. We will examine the mechanics of shareable links, direct permission management, site-based collaboration, and the critical integration with OneDrive. Furthermore, we will delve into the best practices and security protocols that every administrator and power user should implement to prevent data leaks and ensure a productive collaboration environment.
Read: Running Your Own Business: Everything You Need to Know
Understanding File Sharing in SharePoint
To master file sharing, one must first understand the architecture of the SharePoint environment. At its most basic level, SharePoint is a hierarchy of sites, document libraries, folders, and individual files. Permissions typically flow from the top down through a concept known as permission inheritance. When you create a site, the permissions set at the site level automatically apply to all libraries and files within that site, unless specifically broken to create unique permissions for a particular item. This inheritance model is designed to simplify management, but it requires a strategic approach to folder structure and site design.
A common point of confusion for many users is the distinction between SharePoint and OneDrive for Business. While they share the same underlying technology, their purposes differ. OneDrive is intended for individual work—files that are personal to the employee or in an early draft stage. It is essentially your digital briefcase. SharePoint is intended for team or organizational work. It is the digital office cabinet. When a file needs to be accessed by a department or a project group, it belongs in SharePoint. Sharing in SharePoint is therefore more about collective access and long-term storage than the individual-centric sharing found in OneDrive.
Sharing in SharePoint is categorized into two main types: internal and external. Internal sharing involves distributing content to users within your own organization who share the same Microsoft 365 tenant. These users are already authenticated against your corporate directory. External sharing, often referred to as guest access, involves sharing with vendors, clients, or partners. Both types rely on a permission-based model where users are assigned roles such as View, Edit, or Full Control. Understanding these roles is the first step in ensuring that people have the access they need without granting them excessive power over the data.
The hierarchy of SharePoint is essential to grasp because permissions can be managed at any level. However, managing permissions at the file level is significantly more complex than managing them at the site or library level. When you share a single file, SharePoint creates a “unique permission” for that item, effectively breaking the inheritance from the parent folder. While this is necessary for specific tasks, over-using this feature can lead to a “permission mess” where it becomes nearly impossible for an administrator to see who has access to what without clicking through every single file in the library.
Read: Craft Your Winning Business Plan: A Step-by-Step Guide
Method: Sharing Files via Share Link
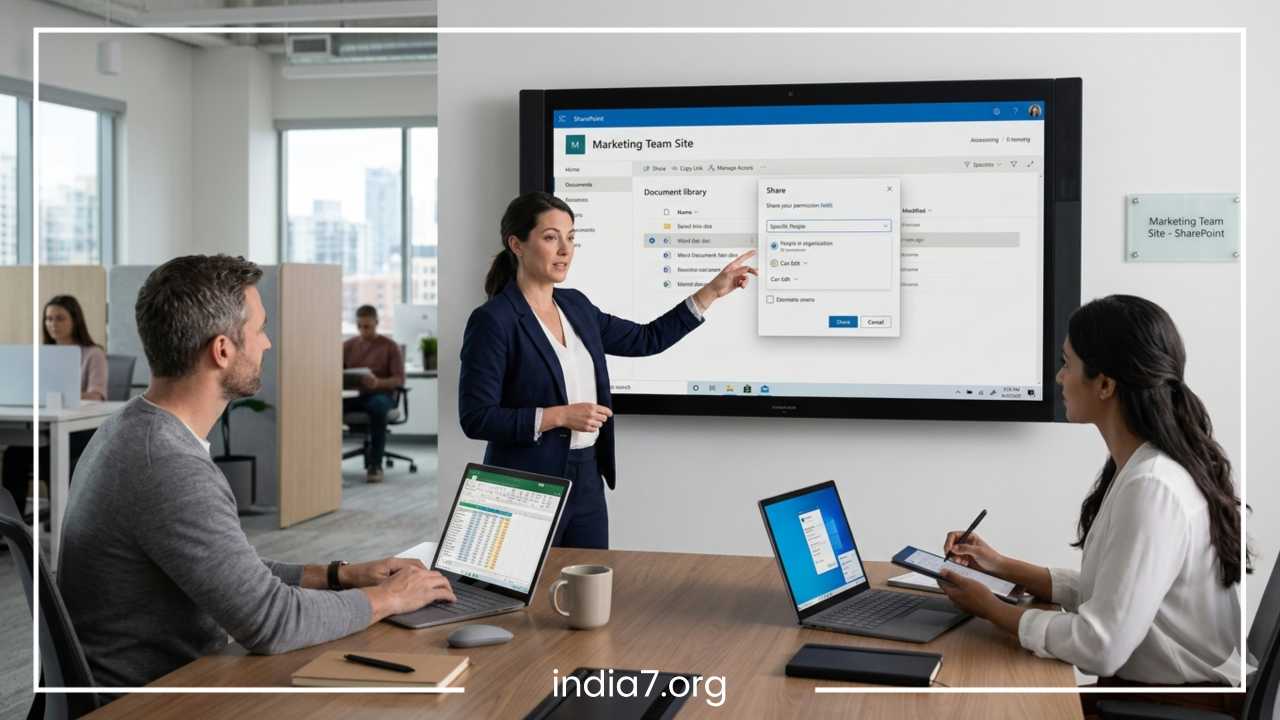
The most prevalent and user-friendly way to distribute content in SharePoint is by generating a shareable link. This method mimics the ease of consumer cloud products while offering granular control over who can access the link and what they can do with it. When you select a file and click the Share button, SharePoint presents a dialog box that allows you to configure the link settings before sending it. This is often the preferred method for ad-hoc collaboration where a formal permission change is not required.
There are several types of links available, and choosing the right one is critical for security. The “Anyone with the link” option creates a public URL. Anyone who obtains this URL can access the file without signing in. This is essentially an anonymous link. Due to the high risk of data exposure, many organizations disable this feature or restrict it significantly. The “People in your organization” link is more secure, as it requires the recipient to be signed into a corporate account within your tenant. This ensures that even if the link is leaked to the internet, only employees can open it.
Finally, “Specific people” is the most secure link type. It restricts access solely to the email addresses you designate. When the recipient clicks the link, SharePoint verifies their identity, usually through a sign-in process or a one-time passcode. This creates a secure bond between the user and the file. Beyond choosing the audience, you can also set specific permissions for the link. You can toggle between “Can view” and “Can edit.” If you choose “Can view,” you also have the option to “Block download,” which forces the user to interact with the file strictly within their web browser. This prevents the file from being saved to a local, unmanaged device.
For higher security, SharePoint allows you to set expiration dates on links. This is a vital feature for project-based work; you can set a link to expire in seven days, ensuring that access is revoked automatically after the immediate need has passed. You can also add password protection to “Anyone” links, providing an extra layer of defense against unauthorized discovery. This method is best used for quick, situational sharing where you do not want to manage permanent permissions or add someone to a formal group.
Read: Biometric Technology: Enhancing Workplace Security
Method: Sharing Files Directly with Users or Groups
While share links are convenient for temporary access, direct permission assignment is the preferred method for structured, long-term collaboration. This method involves explicitly adding a user or a group to the access list of a file or folder without relying on a URL that could be forwarded to others. By assigning permissions directly, you ensure that access is tied to the user’s identity rather than a specific link. This is often managed through the “Manage Access” pane rather than the “Share” dialog.
In this model, you typically work with SharePoint Groups or Microsoft 365 Groups. It is a best practice to avoid adding individual users to files whenever possible. Instead, you should add users to a group (e.g., Marketing Team or Project X Members) and then grant that group access to the necessary resources. This simplifies administration tremendously. If a person leaves the company, removing them from the Microsoft 365 Group automatically revokes their access to every SharePoint resource shared with that group. Conversely, when a new employee joins, they gain immediate access to everything they need by being added to a single group.
The role types in direct sharing are standard: “Read” allows users to view and download; “Edit” allows them to modify, add, and delete files; and “Full Control” allows them to manage permissions for others. There are also custom levels like “Contribute” (edit without deleting) or “Restricted View.” Direct sharing is the superior choice for sensitive internal data or departmental repositories where the membership is relatively stable. It provides a cleaner audit trail and makes it much easier to conduct permission reviews, as you can see exactly who has been granted a specific role on a specific document library without hunting for active links.
Another benefit of direct sharing is the “Check Permissions” feature. Because access is tied to identity, an administrator can run a report to see exactly why a specific person has access to a file. It will show if they have access because they are in the “Owners” group, the “Members” group, or if they were added individually. This level of transparency is essential for compliance in regulated industries like finance or healthcare, where knowing exactly who can see a document is a legal requirement.
Method: Sharing Through SharePoint Sites
Sharing often happens at a much broader level than individual files. In many cases, the most efficient way to share content is to invite a user to become a member of a SharePoint Site. This grants them access to everything within that site’s document libraries by default. This site-centric approach is the foundation of departmental portals and project workspaces. It assumes that if you are part of the team, you should have access to the team’s collective knowledge.
There are two primary types of sites: Team Sites and Communication Sites. Team Sites are generally connected to a Microsoft 365 Group and are designed for active collaboration. When you add a member to a Team Site, they are usually given “Edit” rights to the document library, allowing for fluid co-authoring and file management. Communication Sites, on the other hand, are intended for a one-to-many broadcast of information, such as an HR portal or a corporate news site. In these environments, most users are granted “Read” access, while only a few content owners have “Edit” or “Full Control” rights.
The advantage of site-based sharing is its scalability. Instead of sharing fifty different folders with a new project partner, you simply add them as a guest to the Project Site. However, the limitation of this method is the risk of over-sharing. If a site contains both public project updates and confidential budget spreadsheets, adding someone to the site gives them access to everything unless you manually break inheritance for the confidential folders. Therefore, site-based sharing requires a well-thought-out information architecture.
To balance site-wide access with security, many organizations use “Private Channels” within Microsoft Teams (which are backed by their own unique SharePoint sites) or create “Restricted” document libraries within a larger site. This allows the team to work together in one place while keeping the most sensitive documents behind an extra layer of security. This method is best for established departments, long-term projects, and cross-functional task forces that need a centralized home for all their digital assets.
Method: Sharing via OneDrive Integration
Although SharePoint and OneDrive serve different purposes, they are deeply integrated, and many users find it easier to manage SharePoint files through the OneDrive interface. This integration allows for a seamless flow of data between personal drafts and departmental records. For example, a user can start a document in their OneDrive—their personal workspace—and, once it is ready for the team, use the “Move to” or “Copy to” function to transfer it to a SharePoint document library.
One of the most powerful features of this integration is the Sync capability. By using the OneDrive Sync Client, users can mount SharePoint document libraries directly to their File Explorer on Windows or Finder on Mac. This allows them to share files using the native operating system interface. Right-clicking a file in File Explorer brings up the same SharePoint sharing dialog found in the web browser, providing a consistent experience regardless of where the user is working. This is particularly helpful for users who work with large files or specialized software that doesn’t run in a web browser.
Furthermore, when sharing from OneDrive, the system intelligently recognizes if you are trying to share a file that originated from a SharePoint site. This ensures that organizational policies—such as restricted external sharing or mandatory link expiration—are enforced even when the user is interacting with the file through a desktop sync folder. If an administrator has disabled external sharing for a specific SharePoint site, a user will find the “Anyone” link option greyed out, even if they are right-clicking the file on their desktop.
This integration is best for users who prefer a traditional file-system experience but still need to participate in the robust collaboration environment of SharePoint. It bridges the gap between local productivity and cloud-based governance. However, users must be careful with the “Sync” feature; if they delete a file in their synced File Explorer, it deletes the file for everyone in the SharePoint site. This is where SharePoint’s “Recycle Bin” and version history become vital safety nets.
External Sharing in SharePoint
External sharing is one of the most critical features for modern businesses, but it is also the most complex to manage. It allows you to collaborate with people who do not have a license in your Microsoft 365 tenant. This is usually facilitated through Azure AD B2B (Business-to-Business) collaboration. When you share a file with an external email address, the recipient is often required to enter a one-time passcode sent to their email or sign in with their own Microsoft account, creating a “guest” identity in your directory. This process ensures that you still have control over who is accessing the data.
Administrators have significant control over how external sharing works. They can limit sharing to specific domains (e.g., only allowing sharing with verified partners), prohibit the use of “Anyone” links, or require guests to sign in every few days to maintain their session. From a user perspective, external sharing should be used judiciously. It is ideal for sending deliverables to clients, receiving invoices from vendors, or co-authoring documents with consultants who are not part of your daily staff.
The risks of external sharing involve data residency and the loss of control once a file leaves the walled garden of the internal network. If a user shares a folder with an external partner and that partner’s email is compromised, your data could be at risk. To mitigate this, organizations should encourage the use of “Specific people” links for external parties rather than anonymous links. Regular audits of guest access are also vital; many companies use “Access Reviews” to automatically ask site owners if their external guests still need access every 90 days.
External sharing should be avoided for highly sensitive intellectual property, employee records, or regulated data unless encrypted and managed through more advanced tools like Microsoft Purview Information Protection. For most day-to-day business needs, however, SharePoint’s external sharing is far more secure than sending email attachments, as the file remains in your environment where you can revoke access at any time.
Best Practices for Secure File Sharing in SharePoint
To maintain a secure and efficient SharePoint environment, it is essential to follow the principle of least privilege. This means users should only have the minimum level of access required to perform their jobs. If someone only needs to read a report, do not give them edit access. If they only need one file, do not share the entire folder. This minimizes the “blast radius” if an account is ever compromised.
One of the most effective best practices is to strictly limit the use of “Anyone with the link” sharing. While it is the easiest method, it is also the most dangerous because the link can be indexed by search engines if posted on a public site, or forwarded to unauthorized parties. Organizations should default their sharing settings to “People in your organization” and require a business justification for enabling “Anyone” links. For all links shared externally, setting an expiration date should be a mandatory policy. This ensures that the “back door” to your data closes automatically.
Another key practice is to use Groups rather than individuals for permission management. This reduces the administrative burden and ensures consistency across the organization. For example, if you manage permissions by individual, and a person leaves the company, you have to manually find every file they had unique access to. If you use groups, simply removing them from the group revokes their access across the board. Furthermore, regular permission audits are vital. Site owners should review their “Shared with” reports monthly to see which files are accessible to external guests and revoke access that is no longer necessary.
Enable version control on all document libraries. This allows you to roll back changes if a collaborator accidentally deletes information or overwrites a file. Additionally, monitoring sharing activity via the Microsoft 365 Audit Logs provides visibility into who is sharing what and with whom. This is crucial for compliance and for identifying potential “oversharers” who may need additional training on data security. Educating users on the risks of phishing—where attackers might send fake SharePoint sharing links—is the final and perhaps most important line of defense. A well-informed user is less likely to click a suspicious link or share sensitive data with an unverified external party.
Finally, consider the use of Sensitivity Labels. These labels can be applied to files or sites to automatically enforce sharing rules. For example, a file labeled “Highly Confidential” can be set to prevent any external sharing, regardless of what the user tries to do. This “automation of policy” takes the guesswork out of sharing and ensures that the most important data is protected by default.
Common Mistakes to Avoid
A frequent mistake in SharePoint management is the over-reliance on folders. While folders are familiar to anyone who has used a computer, deep nesting of folders can lead to “URL path length” errors and makes managing permissions incredibly difficult. When permissions are broken at a deep folder level, it becomes hard for administrators to visualize who has access to what, often leading to accidental data exposure. It is better to use metadata (tags) and multiple document libraries to organize files rather than a twenty-layer folder structure.
Another common error is failing to remove old access. Project-based sharing is often “set and forget.” Once a project ends, the external consultant may still have access to the library months later. This “permission creep” is a major security vulnerability. Similarly, many users share entire folders when they only need to share a single file. This grants the recipient visibility into other documents within that folder that may not be intended for them. Always share at the most granular level necessary for the task.
Many organizations also make the mistake of leaving the default sharing settings too permissive. If the global settings are too open, individual site owners might inadvertently share sensitive company data publicly. Conversely, if settings are too restrictive, users will find “shadow IT” workarounds—like using personal Dropbox or Google Drive accounts—to get their work done, which removes the data from corporate oversight entirely. The goal is to find a “goldilocks” zone of security where users can work efficiently without taking unnecessary risks.
Finally, ignoring the “Shared with Me” view and the “Manage Access” pane is a mistake for end-users. Users should be taught how to check who has access to their own files. If a user sees a long list of “Specific people” on a document they no longer wish to share, they need to know how to “Stop Sharing” to clean up those permissions. Cleanliness in permissions is just as important as cleanliness in file organization.
Troubleshooting File Sharing Issues
One of the most common issues users encounter is the “Access Denied” error. This usually occurs when a user tries to access a file via a link that was not intended for them, or if their permissions were revoked. To resolve this, the site owner should check the “Check Permissions” tool within the SharePoint site settings to see exactly what level of access the user has. Often, the user is signed into the wrong Microsoft account (like a personal Outlook account) instead of their work account.
Permission inheritance issues often arise when a folder has “unique permissions.” If a user can see the folder but not the files inside, or vice versa, it is usually because the inheritance was broken and not correctly re-established. Resetting a library to “Inherit Permissions” can often fix these discrepancies, though it should be done carefully to avoid removing intentional access. If you find yourself frequently breaking inheritance, it may be a sign that you need a separate document library or a separate site for that specific content.
If a sharing link is not working, it may have expired or been deleted by the sender. In some cases, the recipient’s organization may be blocking SharePoint links from external tenants due to their own internal firewalls. If an external user cannot access a file despite having a “Specific people” link, ensure they are using the exact email address the link was sent to; guest access is tied to a specific identity, and using an alias or a different personal account will cause the authentication to fail.
Sync conflicts are another common headache. If two people edit the same file offline and then sync, SharePoint may create two versions of the file or prompt the user to choose which changes to keep. Encouraging users to work “online” in the browser or within the desktop app while connected to the internet minimizes these conflicts, as SharePoint’s co-authoring engine can handle real-time changes much more effectively than the offline sync client.
Final Thoughts
Sharing files in SharePoint is a versatile process that offers a range of methods suited for different collaboration scenarios. From the simplicity of shareable links to the robust structure of site-based memberships, the platform provides the tools necessary for modern productivity. However, with great flexibility comes the responsibility of maintaining security. By understanding the nuances of internal and external sharing and adhering to the principle of least privilege, organizations can foster a culture of open collaboration without compromising their digital assets.
Ultimately, the best way to share a file depends on the context of the task at hand. Ad-hoc tasks benefit from links, while long-term projects require group-based site access. Regardless of the method chosen, consistent auditing, user education, and a well-configured administrative backend are the keys to success. SharePoint is not just a storage bin; it is a dynamic collaboration environment. By implementing the best practices outlined in this guide—such as using groups, setting link expirations, and avoiding folder-depth traps—you can ensure that SharePoint remains a secure, organized, and powerful engine for your organization’s collective intelligence. Proper file sharing is the difference between a cluttered, risky digital environment and a streamlined, secure workplace.
Frequently Asked Questions
To further clarify how to navigate the complexities of document collaboration, here are some of the most common queries regarding file management within the Microsoft 365 environment.
How do I share a SharePoint file with someone who doesn’t have a Microsoft account?
You can share files with non-Microsoft users by using the Specific People link or the Anyone with the link option, depending on your organization’s security settings. When you use the Specific People method, SharePoint sends a one-time passcode (OTP) to the recipient’s email address. They must enter this code to verify their identity before they can access the file. This allows you to maintain a secure, tracked connection without requiring the external user to go through a full account registration process.
What is the difference between SharePoint “Copy Link” and “Share” buttons?
The Share button is a proactive tool that allows you to send an email invitation directly from SharePoint and configure specific permissions (View, Edit, Block Download) for designated individuals. The Copy Link button is more passive; it generates a URL based on your default sharing settings which you can then manually paste into a Teams chat, an email, or a document. While both can be used to grant access, the Share menu offers a more comprehensive interface for managing who exactly is receiving that access at the moment of creation.
Why can’t I share SharePoint files externally?
If the option to share with “Anyone” or “Specific People” (outside your organization) is greyed out, it is likely due to tenant-level restrictions set by your IT administrator. SharePoint administrators can disable external sharing globally or for specific sites to prevent data leaks. If you believe you should have this access, you will need to contact your IT department to have external sharing enabled for that specific site collection.
How do I stop sharing a file or folder in SharePoint?
To revoke access, select the file or folder and open the Manage Access pane (usually by clicking the three dots or the “i” icon in the top right). From here, you can see all active links and individuals with direct access. You can either delete specific sharing links or click Stop Sharing at the top of the pane to remove all shared links and delete all users from the access list, effectively reverting the file to its original inheritance settings.
Can I see who has viewed a shared file in SharePoint?
Yes, if your organization has SharePoint Viewers enabled, you can hover over a file to see a statistics card. This card shows the number of views and the names of people who have recently opened the file. For a more detailed audit trail, site administrators can use the Site Usage reports or the Microsoft 365 Audit Logs to track every instance a file was accessed, edited, or shared, providing a complete history of the document’s lifecycle.
What happens to shared links when I move a file in SharePoint?
If you move a file between folders within the same SharePoint site, most modern sharing links will remain intact because the file’s unique ID does not change. However, if you move a file from one site to a completely different site (or from OneDrive to SharePoint), the original sharing links will break. In these cases, you will need to generate new links and re-invite your collaborators to the new location.
How do I share a SharePoint folder without giving access to subfolders?
By default, permissions in SharePoint are inherited. To share a parent folder while restricted certain subfolders, you must navigate to the specific subfolder, open the Manage Access settings, select Advanced, and click Stop Inheriting Permissions. You can then remove the users or groups you do not want to have access to that specific sub-item. However, it is generally considered a better practice to organize your site so that sensitive data and general data live in separate libraries to avoid the complexity of broken inheritance.