Top Ways to Protect from Identity Theft
Top Ways to Protect from Identity Theft | Essential Security Tips
Identity theft is no longer a crime of shadows and alleyways; it has evolved into a sophisticated, high-tech industry that operates across borders, time zones, and encryption layers. At its core, identity theft occurs when a malicious actor gains unauthorized access to your personally identifiable information (PII)—such as your Social Security number, bank account details, credit card information, or even your biometric data—to commit fraud or other crimes. While the concept of impersonation is as old as humanity, the digital revolution has provided bad actors with an unprecedented toolkit to harvest data at a scale previously unimaginable.
In our hyper-connected era, the average person leaves a massive, often permanent digital footprint. Every online purchase, social media post, and login attempt creates a trail of data. For cybercriminals, this data is digital gold, mined through automated scripts and social engineering. According to recent global reports, millions of consumers report identity theft annually, with financial losses reaching into the billions of dollars. However, focusing solely on the dollar amount misses the broader picture. The damage is rarely just financial; victims often face a grueling emotional toll, spending months or even years trying to clear their names, restore their credit scores, and regain their peace of mind.
Read: Avoiding Failure With Your Business Blog
Consider the case of a young professional who applies for a mortgage, only to be rejected because an unknown entity in another state has defaulted on several credit cards in their name. This is the reality of identity theft—it is a silent predator that often goes unnoticed until the damage is profound and life-altering. As we move further into a world dominated by cloud computing, mobile transactions, and artificial intelligence, understanding the mechanics of this threat and implementing robust, layered defenses is not just a recommendation; it is a fundamental necessity for modern survival. To protect yourself, you must move from a passive consumer to an active defender of your own information.
Read: SEO and Business Blogging
Understanding Identity Theft
To defend against identity theft, one must first understand its many faces. It is not a monolithic crime but a spectrum of fraudulent activities tailored to exploit different vulnerabilities in our legal, financial, and medical systems.
Different Types of Identity Theft
-
Financial Identity Theft: This is the most common form, where a thief uses your information to open new credit card accounts, apply for personal loans, or drain your existing bank accounts. The goal is immediate monetary gain, often leaving the victim with a ruined credit history and a mountain of debt they did not incur.
-
Medical Identity Theft: Often overlooked but incredibly dangerous, this occurs when someone uses your name or health insurance member ID to receive medical care, buy prescription drugs, or submit fake billings to insurance companies. Beyond the financial cost, this can result in incorrect medical records—such as a different blood type or allergy being listed—which could lead to life-threatening errors in your own future treatment.
-
Social Security and Tax Identity Theft: Criminals may use your Social Security number to file a fraudulent tax return and claim a refund before you do. They might also use it to gain employment, meaning you could end up owing taxes on income you never earned, leading to complex legal battles with the IRS.
-
Account Takeover: This involves a criminal gaining access to an existing account—such as your email, Amazon, or Netflix—and changing the login credentials to lock you out. Once inside, they can harvest more data, change shipping addresses for purchases, or use your account to launch further attacks on your contacts.
-
Criminal Identity Theft: This happens when someone cited or arrested for a crime provides your name and information to the police. This can result in a warrant being issued in your name, which you may only discover during a routine traffic stop or a background check for a job.
How Identity Thieves Operate
Thieves use a mix of “low-tech” and “high-tech” methods to bridge the gap between your data and their bank accounts. Phishing remains a primary weapon; these are deceptive emails, texts (smishing), or phone calls (vishing) designed to create a sense of urgency. They trick you into clicking a malicious link or revealing a password. Hacking and Data Breaches are more systemic, where criminals infiltrate the servers of large corporations to steal the records of millions of customers at once, which are then sold on the dark web. On the physical side, dumpster diving for bank statements and mail theft remain surprisingly effective ways for criminals to gather PII from those who are less digitally active.
Read: Business Blogging Myths
Common Warning Signs
Vigilance is your first line of defense. Identity theft often leaves clues before the full catastrophe hits. Common warning signs include:
-
Bills for services you didn’t use or products you didn’t buy.
-
Calls from debt collectors regarding accounts or loans you don’t recognize.
-
A sudden, unexplained drop in your credit score or the appearance of unfamiliar inquiries on your credit report.
-
Mail that stops arriving, which could indicate a fraudulent change of address form has been filed.
-
Notification from the IRS that more than one tax return was filed in your name or that you have income from an employer you don’t work for.
Strengthening Digital Security
As we spend an increasing percentage of our lives online, our digital perimeter becomes the front line of defense. A few strategic adjustments to your digital habits can significantly reduce your risk profile.
Passwords and Authentication
The era of using “Password123” or your pet’s name is long gone. Identity thieves use “brute force” attacks—software that tries millions of combinations per second—to crack weak passwords. They also use “credential stuffing,” where they take passwords leaked from one website and try them on thousands of others, banking on the fact that most people reuse passwords.
-
Strong, Unique Passwords: Every account you own should have a unique password that is at least 12 to 16 characters long. It should incorporate a mix of uppercase letters, lowercase letters, numbers, and symbols. A “passphrase”—a string of random words—is often easier to remember and harder for machines to guess.
-
Password Managers: Because no one can remember fifty complex, unique passwords, a password manager is an essential tool. These encrypted vaults generate and store your passwords, so you only need to remember one strong “master key.” They also help identify if one of your passwords has been compromised in a known data breach.
-
Multi-Factor Authentication (MFA): This is perhaps the single most effective tool in your arsenal. MFA requires a second form of verification—such as a code sent to a dedicated app or a biometric scan—to grant access. Even if a hacker manages to steal your password, they cannot enter the account without that second factor. Always opt for an authenticator app (like Google Authenticator or Authy) over SMS codes, as SMS can be intercepted via “SIM swapping” attacks.
Secure Devices and Networks
Your hardware—your phone, laptop, and tablet—is the gateway to your identity. If the device is compromised, your accounts are as well.
-
Regular Software Updates: Developers release updates to patch security vulnerabilities. When you ignore an update for your operating system or browser, you are leaving a known door unlocked for hackers who use automated tools to find unpatched devices.
-
Antivirus and Anti-Malware: Use reputable security software that scans for “keyloggers”—malware that silently records every stroke you type, including passwords and credit card numbers. Modern antivirus also protects against ransomware, which locks your files until a fee is paid.
-
Avoiding Public Wi-Fi for Sensitive Tasks: Public Wi-Fi in coffee shops or airports is notoriously insecure. Hackers can set up “man-in-the-middle” attacks to intercept the data passing through the network. If you must use public Wi-Fi, use a Virtual Private Network (VPN) to create an encrypted tunnel for your data.
Safe Browsing Habits
Common sense and skepticism are powerful filters in a digital environment designed to distract and entice.
-
Checking Website Security: Always look for “HTTPS” in the URL and the padlock icon in the address bar. This indicates that the connection between your browser and the server is encrypted, protecting your data from local eavesdroppers. However, be aware that even malicious sites can now use HTTPS, so it is a sign of encryption, not necessarily a sign of a site’s trustworthiness.
-
Avoiding Suspicious Links and Downloads: If an email from your “bank” or “Amazon” feels overly urgent, contains typos, or uses a generic greeting like “Dear Customer,” do not click the links. Instead, go directly to the official website by typing the address yourself or use the official mobile app.
Protecting Personal Information Offline
While the world is increasingly digital, the physical world still poses significant risks. Traditional “analog” theft remains a staple for identity criminals because many people let their guard down when dealing with paper and physical objects.
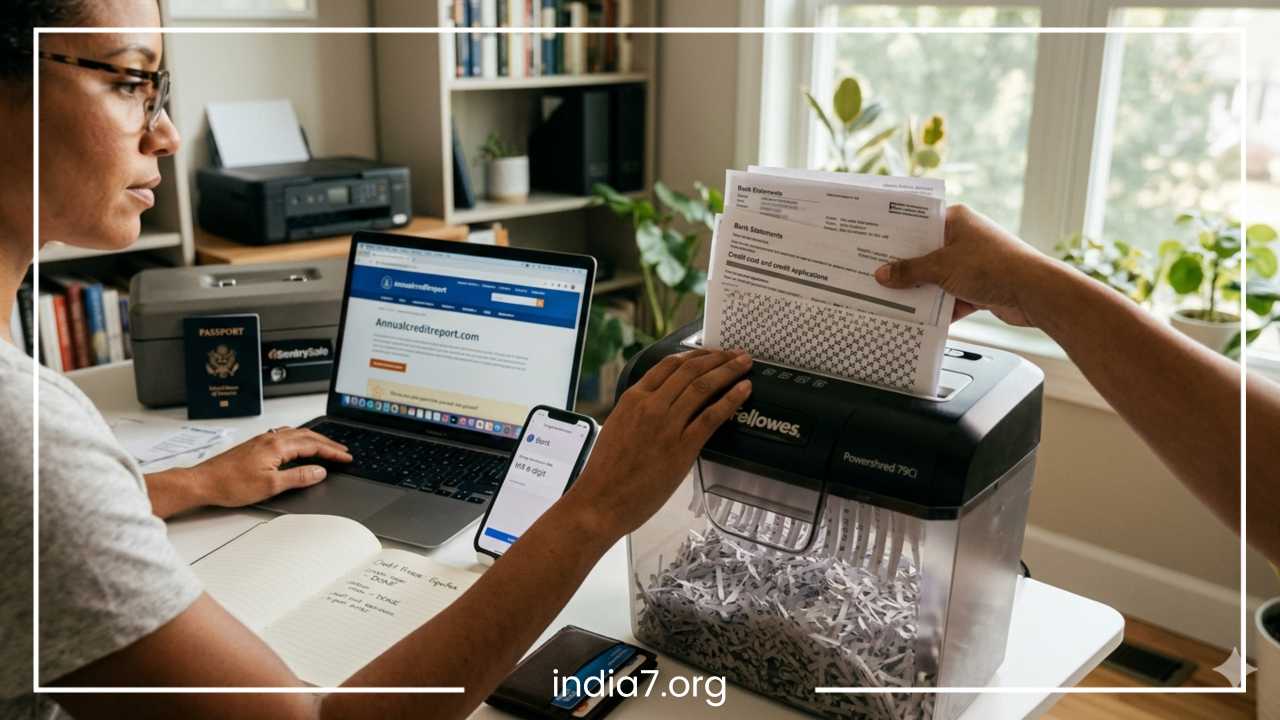
Shredding Sensitive Documents
Your trash is a treasure trove for an identity thief. Old bank statements, pre-approved credit card offers, utility bills, and even medical receipts contain enough information—names, addresses, and partial account numbers—to start building a fraudulent profile or to convince a customer service representative that the thief is actually you. Invest in a high-quality cross-cut shredder and make it a habit to destroy any document that contains PII. Never simply toss mail into the recycling bin intact.
Securing Personal Mail
Secure your mailbox as if it were a bank vault. Outgoing mail containing checks or sensitive applications should never be left in an unlocked residential mailbox for the mail carrier to pick up. This is a prime target for “mail fishing,” where thieves steal envelopes to wash checks or harvest data. Always drop sensitive mail off at a post office or a secure blue collection box. For incoming mail, try to collect it as soon as it is delivered. If you are going on vacation, have the post office hold your mail so it doesn’t pile up, signaling your absence to potential thieves.
Caution in Public and Professional Spaces
Be mindful of “shoulder surfing”—criminals looking over your shoulder at an ATM, at a checkout counter, or while you fill out forms at a doctor’s office. At work or school, don’t leave your laptop or smartphone unattended. Even in a seemingly safe office environment, an unlocked screen is an invitation for data theft.
Social events can also be risky; avoid sharing overly personal details with new acquaintances. Information like your mother’s maiden name, the name of your first pet, or your childhood street are common security questions for online accounts. A thief doesn’t need to hack your computer if they can simply chat you up at a party and get the answers to your security questions.
Protecting Wallets and IDs
Your Social Security card should never be kept in your wallet. It is the “master key” to your identity and should be stored in a secure, fireproof safe at home. Similarly, only carry the credit cards and IDs you plan to use for that specific day. If your wallet is lost or stolen, the fewer items the thief has access to, the less damage they can do and the fewer calls you will have to make to cancel services.
Financial Security Measures
Financial institutions have sophisticated fraud detection algorithms, but they are not foolproof. You are the primary custodian of your wealth and the first person who will notice when something is wrong. Active management of your financial footprint is crucial.
Monitoring Bank and Credit Card Statements
You should review your bank and credit card statements at least once a week. In the age of mobile banking, this takes only a few minutes. Look for small, “test” transactions of a few cents or a dollar. Thieves often use these micro-transactions to see if a stolen card number is active and valid before they attempt a large, high-value purchase. If you see a charge for a merchant you don’t recognize, investigate it immediately.
Setting Up Transaction Alerts
Most modern banks and credit card issuers allow you to set up real-time notifications. You can receive a text or push notification for:
-
Any purchase over a certain dollar amount (e.g., $50).
-
Any “card-not-present” transaction (online or phone orders).
-
International transactions.
-
Declined transactions.
These alerts allow you to catch fraud the very second it happens, often enabling you to stop a thief before they move on to a second or third store.
Freezing Credit Reports vs. Fraud Alerts
If you do not plan on applying for a mortgage, an auto loan, or a new credit card in the near future, a credit freeze is the single most powerful protection available. It prevents lenders from accessing your credit report, which effectively stops identity thieves from opening new accounts in your name because lenders won’t issue credit without seeing that report. It is free to implement at all three major bureaus (Equifax, Experian, and TransUnion) and can be “thawed” temporarily via a secure PIN when you actually need to apply for credit.
A fraud alert is a less restrictive alternative. It tells businesses that they must take extra steps to verify your identity before issuing credit. This is useful if you are actively shopping for a loan but want an extra layer of security.
Using Credit vs. Debit Cards
For online shopping and even in-person dining, use a credit card instead of a debit card whenever possible. Credit cards offer vastly superior legal protections under federal law (such as the Fair Credit Billing Act). If a credit card is compromised, you are generally not liable for the fraudulent charges while they are being investigated, and no money has actually left your bank account. If a debit card is compromised, the money is gone from your checking account immediately. While you may eventually get it back, the weeks-long investigation could leave you unable to pay rent or buy groceries.
Social Media and Online Presence
Social media is a double-edged sword. While it connects us to friends and family, it also provides a detailed blueprint for identity thieves to “social engineer” their way into our lives. Information that seems harmless to you is data to a criminal.
Limiting Personal Information Shared Online
Thieves use social media to find the answers to your “secret” security questions. If your profile lists your exact birthday, your high school, your pet’s name, and photos of your children, you have essentially handed over the keys to your accounts. Avoid posting photos that show the front of your house with the address visible, or photos of travel tickets, concert stubs, and passports, all of which contain scannable barcodes or sensitive numbers.
Privacy Settings and Controls
Regularly audit your privacy settings on platforms like Facebook, Instagram, and LinkedIn. Ensure that your posts, friend lists, and contact information are only visible to “Friends” rather than the general public. However, always operate under the assumption that “private” is a relative term; anything you post online can be screenshotted and shared by someone else. If you wouldn’t want it on a billboard, don’t put it on social media.
Avoiding Quizzes and Third-Party Apps
Beware of viral social media quizzes (e.g., “What is your ‘Rockstar’ name? It’s your first pet + the street you grew up on!”). These are often thinly veiled data-harvesting operations designed to gather answers to security questions. Similarly, be cautious about using your Facebook or Google account to sign into third-party apps or games. These apps often request permission to “view your profile” and “access your friends list,” giving them a direct pipeline to your personal data.
Being Cautious with Contacts
Be skeptical of friend requests from people you don’t know, but be even more skeptical of “duplicate” requests from people you are already friends with. This is a common tactic where a thief clones a friend’s profile and then sends you a message with a “must-see video” link that is actually malware. If a friend sends you an unusual message or asks for money, call them on the phone to verify before clicking or responding.
Responding to Identity Theft
If you become a victim of identity theft, the initial shock can be paralyzing. However, a swift, organized, and documented response can drastically contain the damage and shorten the recovery time.
Steps to Take Immediately
-
Contact Financial Institutions: Call the fraud department of any bank or credit card issuer where you suspect unauthorized activity. Close or freeze those accounts immediately to prevent further charges.
-
Place a Fraud Alert or Credit Freeze: Contact one of the three major credit bureaus; by law, once you place an alert with one, they must notify the other two. This ensures no further accounts can be opened while you are in recovery.
-
Report to the Federal Trade Commission (FTC): Visit IdentityTheft.gov. This is a comprehensive resource that helps you create a recovery plan and generates a formal “Identity Theft Report.” This report is your legal proof that your identity was stolen.
-
File a Police Report: While local police may not have the resources to track down a digital hacker in another country, a formal police report is often required by banks, insurance companies, and credit bureaus to officially dispute fraudulent accounts and debts.
Documenting Everything
Restoring your identity is a process of “paperwork warfare.” You must keep a meticulous log of every action you take.
-
Keep a notebook dedicated to your recovery.
-
Record the date, time, and the name/ID number of every customer service representative you speak with.
-
Follow up every phone call with a letter or email summarizing what was discussed and agreed upon.
-
Save copies of all letters, reports, and receipts for expenses related to the theft (some identity theft insurance policies or homeowners’ insurance may reimburse these costs).
Restoring Your Identity Over Time
Recovery is a marathon, not a sprint. You will need to send copies of your Identity Theft Report to every creditor where a fraudulent account was opened to have the debt wiped. You must also contact the credit bureaus to ensure these items are removed from your credit history. Check your credit reports again three months, six months, and one year after the incident to ensure no “zombie” accounts—old fraudulent accounts that were sold to different debt collectors—have reappeared.
Emerging Technology and Future Risks
The battleground of identity theft is constantly shifting. As security professionals develop better ways to protect consumers, thieves develop better exploits to bypass them.
Rise of AI-Generated Attacks
Artificial Intelligence is changing the game for phishing. In the past, phishing emails were often easy to spot due to poor grammar and clunky formatting. Today, AI can generate perfectly written, highly personalized emails at scale. Even more concerning is the rise of “Deepfake” technology. Criminals can now use a short clip of someone’s voice—harvested from a social media video—to create an AI voice clone. They then call a family member or an employee, sounding exactly like a loved one or a CEO, to trick them into transferring funds or revealing passwords.
Biometrics and Digital Wallets
On the defensive side, technology is also improving. The shift toward biometric authentication (fingerprints and facial recognition) and digital wallets (like Apple Pay or Google Pay) offers much higher security than traditional physical cards. Digital wallets use “tokenization,” meaning your actual credit card number is never stored on your device or shared with the merchant. Even if a store’s database is hacked, the thief only gets a one-time-use token that is useless for future purchases.
Staying Ahead with Cyber Awareness
The most important tool you have is your own awareness. Stay informed about the latest scams by following updates from the FTC or cybersecurity news sites. Understand that technology is a tool, and like any tool, its safety depends on the person using it.
Final Thoughts
Identity theft is a persistent and evolving threat, but it is not an inevitable one. While you cannot control when a large corporation suffers a data breach, you can control how much of your data is available to the world and how difficult you are to exploit.
Summary of Protective Measures
-
Layer Your Digital Defense: Use unique passwords, a password manager, and always enable Multi-Factor Authentication.
-
Secure Your Physical Footprint: Shred everything, lock your mailbox, and never carry your Social Security card.
-
Actively Manage Finances: Set up transaction alerts and use a credit freeze if you aren’t seeking new credit.
-
Audit Your Social Presence: Treat your personal details like a guarded secret, not a public broadcast.
Identity theft prevention is not a one-time task that you can check off a list and forget. It is an ongoing practice of proactive vigilance and a healthy sense of skepticism. In a world where your information is the most valuable currency, protecting your identity is the single best investment you can make in your future financial stability and personal peace of mind. By taking these steps today, you ensure that you remain the only person who can claim to be you.